Reports show a growing number of DDoS attacks, what are your options?

Knowledge blog

Worldwide DDoS attacks are up, both in size and in volume. According to several reports, there has been an increase in DDoS attacks on all metrics. An explanation can be found in the fact that attacks are becoming easier to execute, which makes them accessible to anyone. It sounds concerning, but if we understand the cause, isn’t there a solution?
Every year DDoS attacks increase in both size and volume
Last year the NBIP foundation shared their DDoS report on attacks in 2019. Their anti-DDoS service (NaWas) protects 43% of all Dutch domains. If we look at their findings from the report we see a trend of larger attacks and an increase in their complexity. But not in numbers. The foundation found a slight decrease compared to the previous year. If we look at a report of the same year by Neustar, which is based in the United States, they conclude the same overall. The only difference in their statistics was that worldwide, DDoS attacks were actually up by 180% overall compared to 2018.
In 2020 we have found ourselves confined to our homes due to a global pandemic. It is not surprising that during this period internet traffic is up. Following up on the statistics of the previous year, we see that the pandemic has had a snowball effect on the spread of DDoS attacks. While statistics from 2019 already showed a trend in increased DDoS attacks, the first half of 2020 did not look better. Neustar compared numbers to the same period of the previous year and concluded that DDoS attacks increased by more than two and a half times. Reports from other sources, like Nexusguard and Netscout underline these numbers.
But that is not all, the attacks grew in size as well. Where a mitigation of 587 Gbit/s was a record in 2019 for Neustar, the largest attack in 2020 was mitigated at 1.17 Tbit/s. Coincidentally Amazon mitigated an even bulkier attack (2.3 Tbit/s) in June of 2020. The first six months of 2020 brought us bigger, longer, and more complicated attacks. If we take the numbers at face value this raises the question: how will we be able to equip us against growing DDoS attacks?
From a complicated cyberattack to a simple transmission that anyone can launch
According to the NBIP report smaller attacks (less than 1 Gbit/s) are in decline, which is based on the common notion of a DDoS attack; a net of computers linked together (botnet) to disrupt a service. This brings us to the multiple ways of denying service. The most concerning being that a majority of recent attacks was able to circumvent application layer firewalls. Smaller attacks are typically designed to target a specific application or website. Once the smaller attack is successful it allows for another type of attack. Combining DDoS attacks are considered multivector. These can seem complex, but are usually a mix of common attacks.
According to a study in 2010 it is possible to outright buy a DDoS attack. The study stated that it costs around $67 a day. A more recent study by Kapersky underlined that $25 dollar gets you an attack of one hour. Which is a quick and relative cheap solution to bringing a service offline. But even without a third party there are several straightforward options. Sending a ping flood to someone’s IP address or installing a tool like Low Orbit Ion Cannon. Which can be done by anyone. But to be honest, it isn’t called straightforward without a reason. If you have any kind of protection, an attack like that has little to no effect.
If you have a service that needs to be online 24/7, consider protection
No organizational unit can mark itself completely safe from DDoS attacks as we can conclude there has been an increase all round. In size, in volume, and in complexity. But that doesn’t mean we aren’t able to mitigate and thus prevent DDoS attacks altogether. It starts with identifying the need for protection, which is a must if you have any type of service that has to be online all year round. To ensure that your services are protected without equipping yourself with expensive equipment, start with asking yourself if your IT-infrastructure is capable of mitigating DDoS attacks. Involving an external party just might be the solution.
The majority of Dutch internet providers use the DDoS service NaWas of the NBIP foundation. It is relatively expensive to acquire, develop, and setup an anti-DDoS appliance. This is the main reason that protection through a third party is more common than having your own. Whereas expensive appliances are usually tied to only one node Worldstream offers a more horizontal approach and thus multiple nodes. In the last few years Worldstream has developed their own DDoS platform, Worldshield, which is an unique anti-DDoS system that is tied to our IT-infrastructure. Which means that it can only be applied to our own network and is exclusive to our customers. It is part of a solution that encompasses infrastructure as a service. Worldshield is specifically meant for IT-professionals that want to have their entire infrastructure in one place.
But how does Worldshield again protect against DDoS attacks? In order to deflect DDoS attacks we monitor all incoming traffic at the core routers. These routers send sFlow data, which is analyzed in real-time in order to recognize patterns. If an anomaly is detected this is rerouted to the Worldshield cluster. Combined attacks like an UDP amplification and SYN flood (layer 3 and 4) can be mitigated by our Worldshield. The actual mitigation is handled automatically. The utilization rate of our network (45%) translates to our ability to offer mitigation to attacks of 1 Tbit/s and beyond.
The presence of DDoS attacks will remain a threat to internet activity as a whole. It will not go away by creating one method that fits all. As DDoS attacks adopt so do we. Be aware of the disruptive ability of DDoS attacks. Even a simple attack can bring your business offline. It will not cause any long term damage. But if staying online is your main priority, the risk of losing connectivity is greater than losing data.
Did you know that our Worldstream DDoS Shield has more options? Read more about our platform on DDoS Protection.
You might also like:
- Public or Private Cloud, how do you choose strategically?
- Does switching to the cloud complement your IT infrastructure?
- Are Dedicated Servers Still Relevant? We Give 6 Reasons.
Have a question for the editor of this article? You can reach us here.

Latest blogs
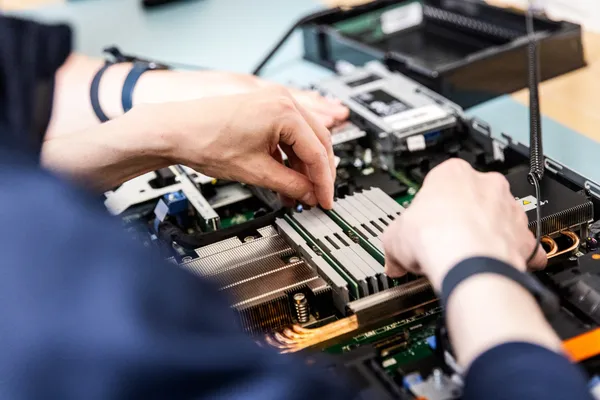
AMD EPYC 4465P dedicated server: serious power without unnecessary complexity

Knowledge blog

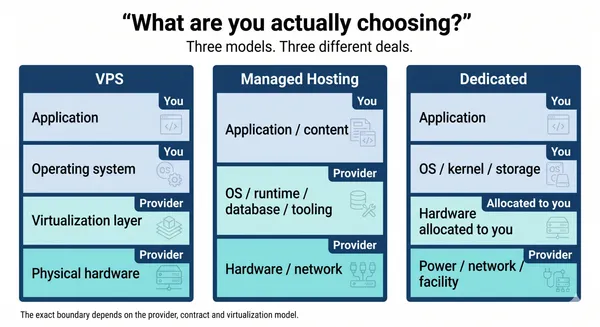
VPS, Managed Hosting, or Dedicated: What You Are Actually Choosing in 2026
Knowledge blog
The 4 Elements of the Worldstream DNA

Knowledge blog

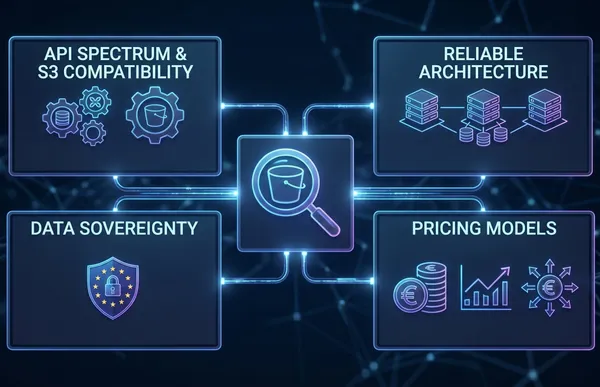
S3 Object Storage in Europe: What to Evaluate Before You Store a Single Byte

Knowledge blog
DDR5 Memory Prices Surged 307%. Here Is What That Means for Your Infrastructure Budget.

News
Pricing update. Price adjustment effective May 1, 2026

News